Website security: how to secure WordPress
Website security: how to protect Wordpress and prevent you from falling victim to a hacker or other attacker.
di Antonio Lamorgese
Given the importance of the topic, today I will discuss, through examples and advice, the most innovative systems to ensure the website security managed with the number one CMS in the world: “WordPress”. Securing WordPress is an operation of fundamental importance for a developer.
Table of contents...
1. Why secure a website?
Setting up a website, a blog or, even a web application, involves enormous sacrifices for a developer. So, regardless of the size of the website, the security of a website is one of the primary aspects to be addressed. It goes without saying that, if you develop websites, for a living, you must always be updated on useful tips and practices, aimed at making a website safe.
However, a hacker has several well-established techniques at his disposal to threaten a website. In this guide I will tell you what to do and how to prevent your website, managed by WordPress, from completely falling into the hands of a hacker.
READ MORE: How to install Windows 11 on Raspberry Pi 4
2. How to ensure WordPress security
Before going into the recommended practices for the security of a site, it is necessary to reiterate that WordPress is always updated to the latest version. To do this, it is not necessary to be an expert programmer but, when the CMS gives us directions, through its bulletin board, to do so, all we have to do is click on the appropriate button in the administration dashboard and update WordPress without fear.
Not only that, one of the many aspects that many overlook and that some web service providers do not keep the PHP version up to date. Unfortunately, this is an operation that cannot be performed from the WordPress bulletin board but must be changed directly from the control panel, made available by the provider, on the domain setup and management page.

The figure shows the procedure that can be carried out, directly by the user, on Aruba.it hosting, to update the PHP version to the most recent one available.
3. How to prevent a brute force attack
Yes, it is not a poorly written sentence, indeed, it is one of the most widespread attacks on the web. That is, a user or, even worse, a bot, are continuously trying to access your website, trying to guess, through well-known techniques, your username and password to access WordPress.
Logically, these attempts are made by the hundreds if not thousands, within a second. In these cases, in addition to maintaining password management, making them as secure and complex as possible. It is necessary to prevent, even for administrative users, the permission to modify files related to themes and plugins, directly from the WordPress administration page.
To do this, you need to insert this line of code in the wp-config.php file:
define('DISALLOW_FILE_EDIT', true);After updating the wp-config.php file, as required, you need to install and activate an absolutely unique and free plugin. The Plugin in question is “Limit Login Attempts”.
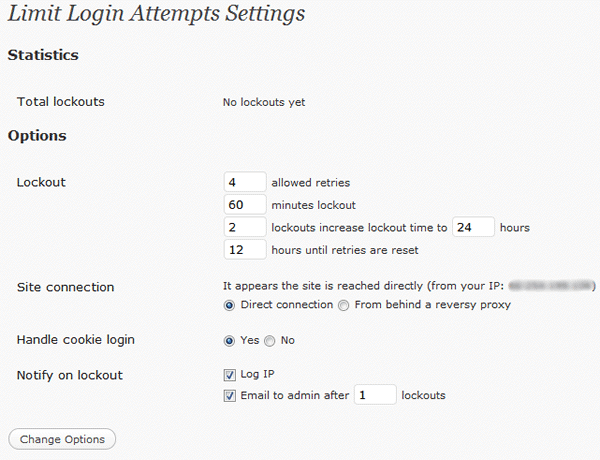
This plugin counteracts any type of brute force attack, limiting access attempts to a number predetermined by us. Therefore, in the event of an error accessing WordPress, the plugin would block the user for a time, also set by us. Unfortunately, WordPress, by default, does not limit attempts to access the website’s administration page.
4. How to force WordPress login via SSL
When we send data to the server, such as username and password, the server will receive this data in the clear. It is logical that this type of data transmission is not the best. It is therefore possible to force WordPress to transmit any type of data, using a protocol that is widely used today, the SSL protocol.
To force WordPress to this type of transmission and management of credentials between server and browser, all you have to do is insert these two lines of code in the wp-config.php file:
define('FORCE_SSL_ADMIN', true);
define('FORCE_SSL_LOGIN', true);5. Conclusions
What I have covered in this guide, represent the minimum practices, but of great impact, regarding the securing of a website and WordPress. In this video tutorial, which I recommend you follow, WordPress security is managed by installing a free plugin, which is also unique in its kind. The plugin in question is WordFence.

